Identity Trend 7: Regulation and Compliance
This post is the seventh in a series of eleven posts I am writing about key trends in the Identity Management industry.
 Government regulations have been enacted to address problems problems with fraud, governance, security and privacy arising in various industries. For example, the Sarbanes-Oxley Act of 2002 (Sarbox) was intended to make corporate governance practices more transparent and to improve investor confidence. It addressed financial control and financial reporting issues raised by the corporate financial scandals, focusing primarily on two major areas: corporate governance and financial disclosure.
Government regulations have been enacted to address problems problems with fraud, governance, security and privacy arising in various industries. For example, the Sarbanes-Oxley Act of 2002 (Sarbox) was intended to make corporate governance practices more transparent and to improve investor confidence. It addressed financial control and financial reporting issues raised by the corporate financial scandals, focusing primarily on two major areas: corporate governance and financial disclosure.
Government regulations tend to become more complex and far-reaching over time. For example, to address the challenges of security and privacy, the Health Insurance Portability and Accountability Act (HIPAA) was enacted by Congress in 1996 to establish national standards for use of health care records. HIPAA provided a foundation upon which multiple regulations have been based to address issues with the administration and protection of sensitive medical records information.
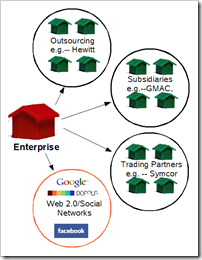
Title XIII of the American Recovery and Reinvestment Act of 2009 (ARRA), also known as the Health Information Technology for Economic and Clinical Health Act (HITECH) includes a section that expands the reach of HIPAA by introducing the first federally mandated data breach notification requirement and extending HIPAA privacy and security liability to business associates of "covered entities" (generally, health care clearinghouses, employer sponsored health plans, health insurers, and medical service providers that engage in certain transactions on behalf of individuals).
The current trend to more extensive government regulation of industry will likely continue or escalate, placing additional burden on enterprises to comply with increasingly complex compliance mandates.
 A second source for industry regulations comes from industry itself. For example, the Payment Card Industry (PCI) Data Security Standard (DSS) is a global security standard for safeguarding sensitive credit card data. This standard was established by PCI Security Standards Council, an organization founded by industry leading enterprises: American Express, Discover Financial Services, JCB International, MasterCard Worldwide, and Visa, Inc. The standard was created to help organizations that process card payments prevent credit card fraud through increased controls around data and its exposure to compromise.
A second source for industry regulations comes from industry itself. For example, the Payment Card Industry (PCI) Data Security Standard (DSS) is a global security standard for safeguarding sensitive credit card data. This standard was established by PCI Security Standards Council, an organization founded by industry leading enterprises: American Express, Discover Financial Services, JCB International, MasterCard Worldwide, and Visa, Inc. The standard was created to help organizations that process card payments prevent credit card fraud through increased controls around data and its exposure to compromise.
Identity and Access Management (IAM) is a critical enabler for compliance with government and industry regulations. For example, Sarbox requirements for fraud reduction, policy enforcement, risk assessment and compliance auditing are supported directly by IAM technology and methods. By streamlining the management of user identities and access rights, automating enforcement of segregation of duties policies, and automating time-consuming audits and reports, IAM solutions can help support strong security policies across the enterprise while reducing the overall cost of compliance.
Similarly, IAM technology and processes, which control user access to data, applications, networks and other resources, can directly support HIPAA/HITECH requirements for privacy, security, auditing and notification.
Recommendations:
Practical experience in the field gained as many enterprises have implemented IAM systems to support compliance efforts has yielded several recommended best practices for implementing IAM systems to enable HIPAA/HITECH compliance. The following list of best practices will be explored in more detail in a subsequent blog post:
- Understand regulatory requirements that apply to your enterprise.
-
Recognize IT’s critical role in the compliance process.
-
Understand the role of IAM in supporting compliance.
-
Think of compliance as a long-term program, not a single project.
-
Establish compliance policies. principles should be documented as a foundation upon which to build policies, practices and strategies.
-
Develop a business-driven, risk-based, and technology-enabled compliance strategy.
-
Collaborate with your business partners and associates.
-
Establish a governance process.
-
Implement your strategy in phases.
-
Follow established standards.
-
Give real-time visibility into compliance status, progress and risks.
-
Unify disparate compliance efforts.
-
Assess progress and adjust as necessary.


 It is always enjoyable to read advice from those in the trenches of Identity management implementation. As a recent guest blogger on the Identigral blog,
It is always enjoyable to read advice from those in the trenches of Identity management implementation. As a recent guest blogger on the Identigral blog,